Experience the Future of Contextual Marketing with Yarnit AI
At Yarnit, we understand that the security of your data is paramount. As an enterprise-grade AI marketing platform, we prioritize safeguarding your information through a comprehensive security program. Our commitment to protecting your data from unauthorized access, use, and disclosure ensures that your content creation processes remain both secure and efficient.















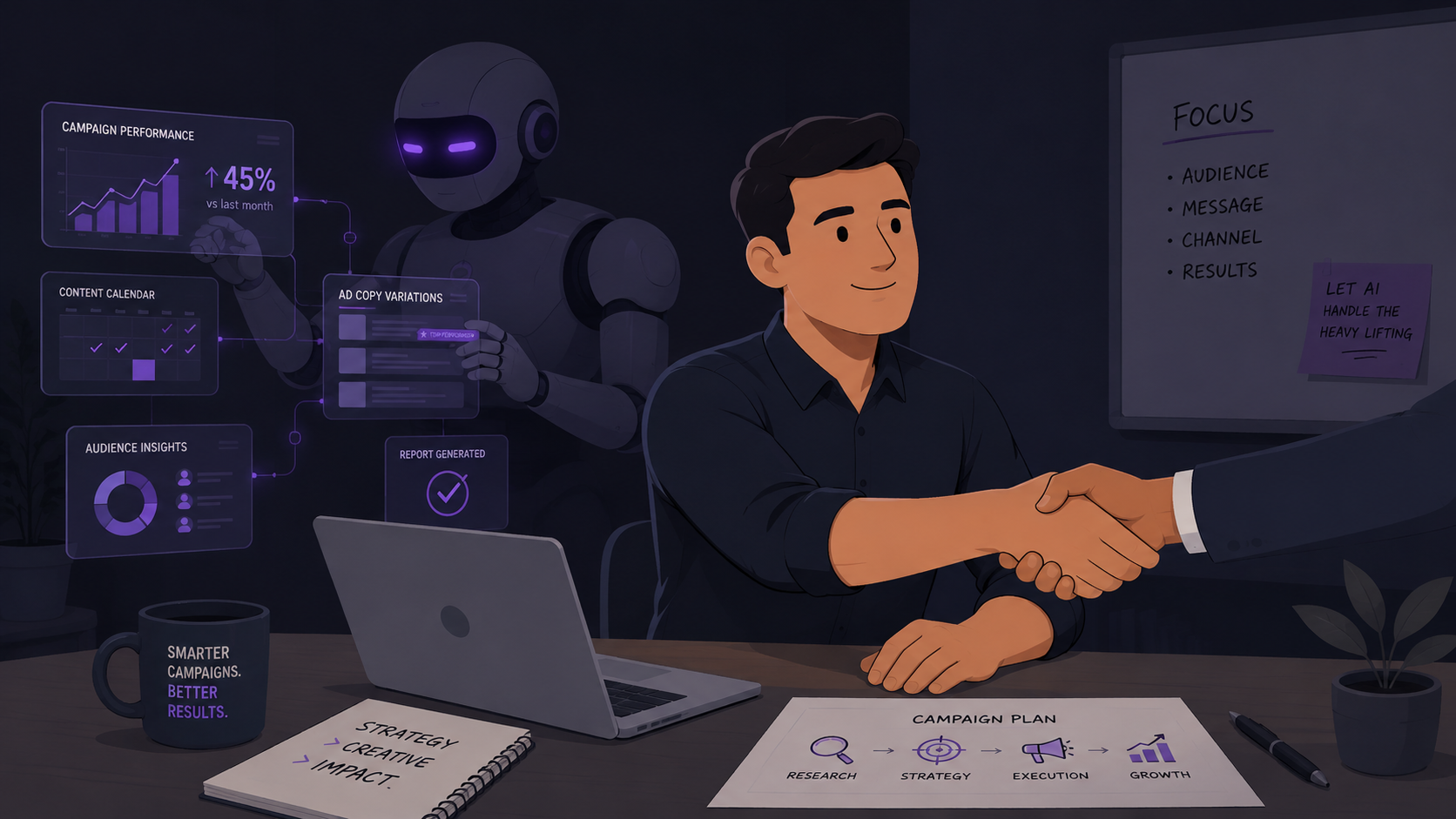
.jpg)






